Limit Cronofy's access
Read as MarkdownCronofy’s access can be limited to only specific users’ calendars by configuring an ApplicationAccessPolicy within your Office 365 Exchange tenant.
Configuring an ApplicationAccessPolicy #
To configure an application access policy and limit the scope of Cronofy’s application permissions:
Connect to Exchange Online PowerShell. For details, see Connect to Exchange Online PowerShell
Cronofy application’s ID for Microsoft 365 Enterprise Connect via Graph is:
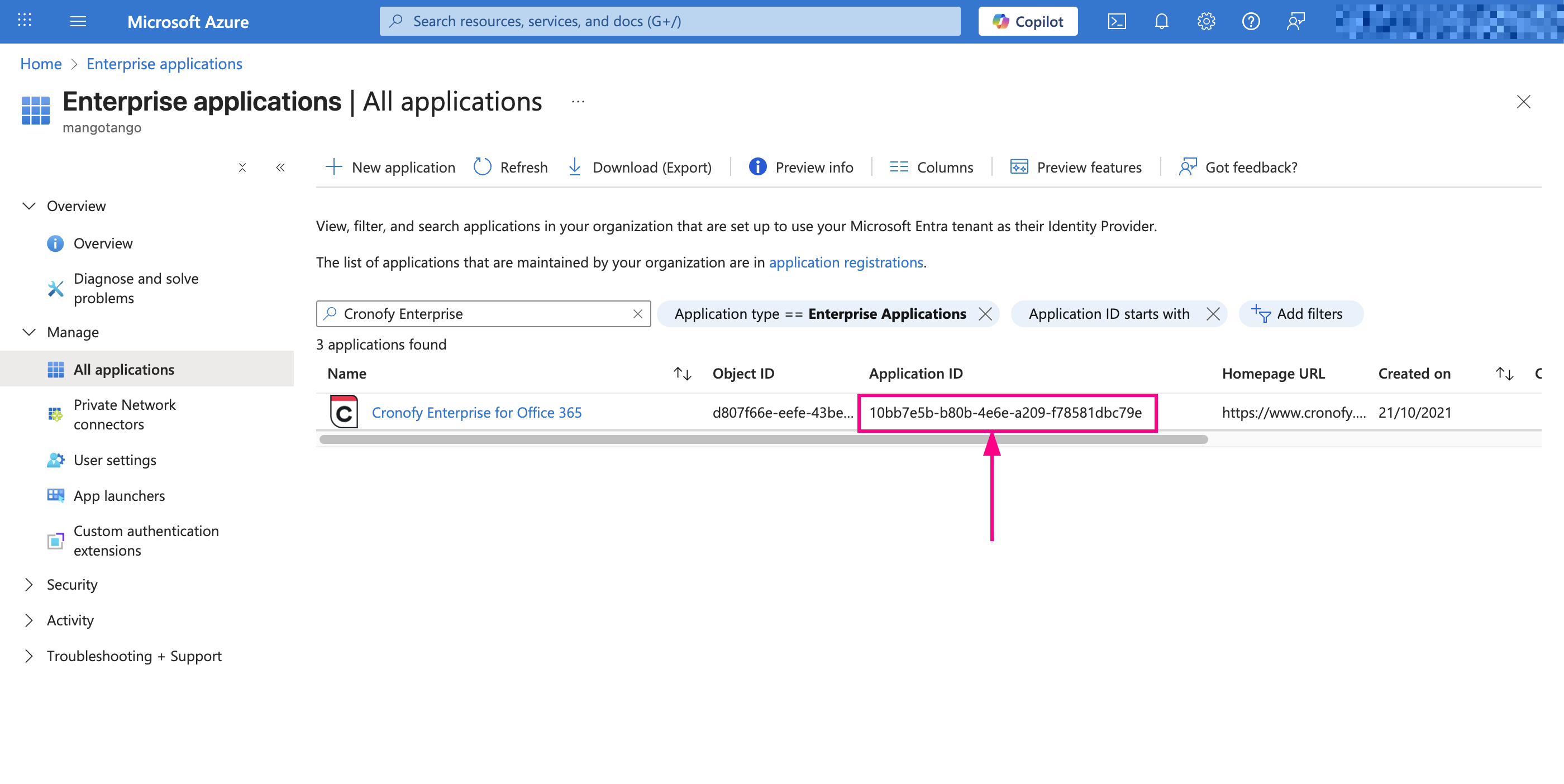
10bb7e5b-b80b-4e6e-a209-f78581dbc79e. If you wish to verify this, you may do so as follows:If you have already authorized your connection, you may confirm this by visiting the Azure Active Directory Enterprise application portal as seen below.
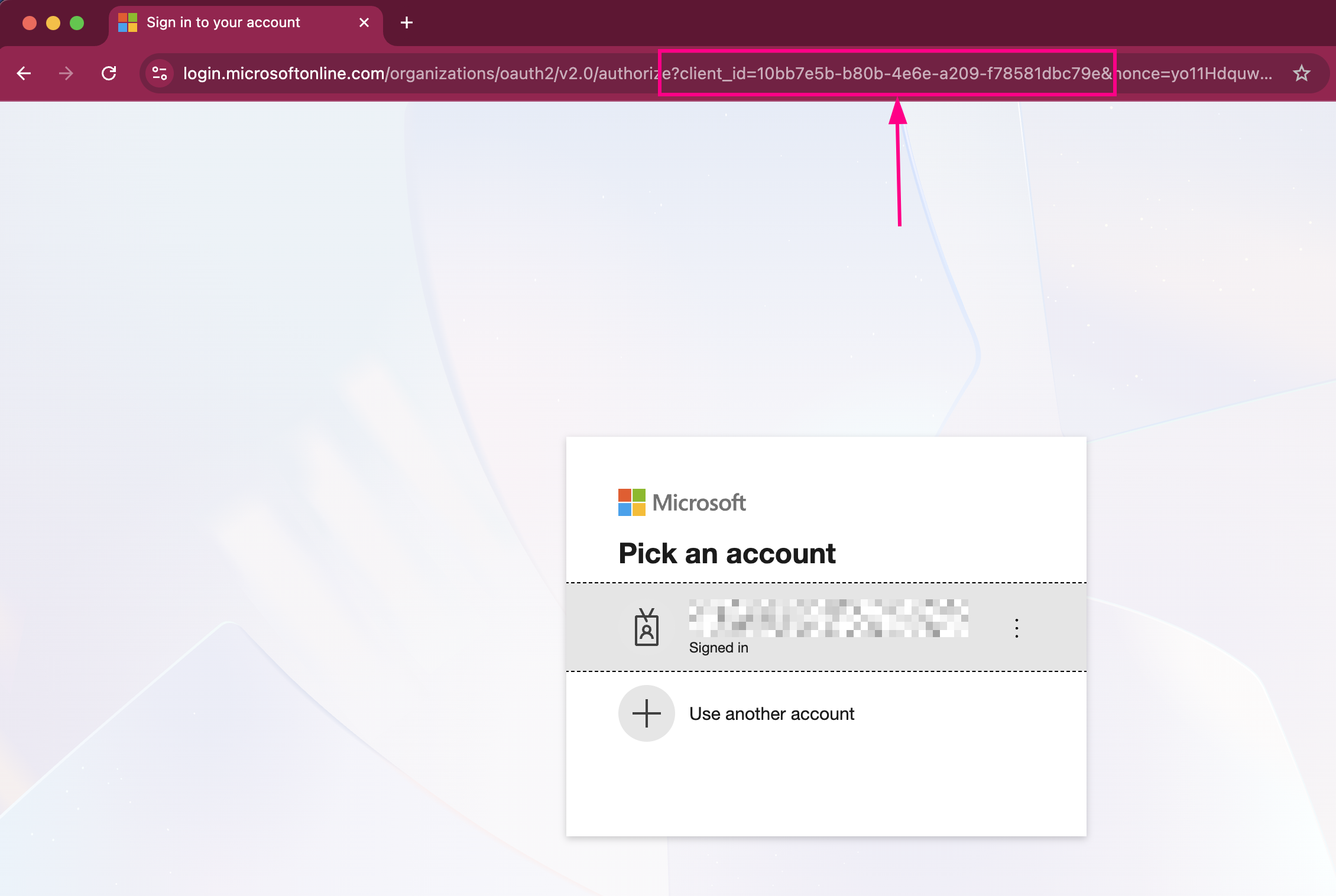
If you have not yet authorized the connection, you can see the application ID visible in the address bar when initiating (but without completing) the connection:
Create a new mail-enabled security group or use an existing one and identify the email address for the group.
Note: Currently, mail-enabled security groups must be created from Exchange Admin center or Classic Exchange Admin Center to take action. Security groups created from Azure itself won’t get reflected on Exchange Online and therefore, you wouldn’t be able to use those groups as part of the ApplicationAccessPolicy.
Create an application access policy. Run any of the following commands, replacing the arguments for PolicyScopeGroupId, and Description.
4.1. RestrictAccess, means that only members of the support@contoso.com mail-enabled security group will have access to the AppId
New-ApplicationAccessPolicy -AppId 10bb7e5b-b80b-4e6e-a209-f78581dbc79e -PolicyScopeGroupId support@contoso.com -AccessRight RestrictAccess -Description "Restrict this app to members of the Support group."4.2. DenyAccess, means that members of the support@contoso.com mail-enabled security group will NOT have access to the AppId
New-ApplicationAccessPolicy -AppId 10bb7e5b-b80b-4e6e-a209-f78581dbc79e -PolicyScopeGroupId support@contoso.com -AccessRight DenyAccess -Description "Deny this app to members of the Support group."Test the newly created application access policy. In this example we used a member of our support team. Depending on whether you set a Restrict or Deny Access Policy, the Grants result may vary.
Test-ApplicationAccessPolicy -Identity support_user1@contoso.com -AppId 10bb7e5b-b80b-4e6e-a209-f78581dbc79e
Note: Changes to application access policies can take up to 30 minutes to take effect, based on Microsoft’s documentation.
Additional reading #
For further reading on the mechanism mentioned in this article, please see this documentation from Microsoft.
If you require any further assistance, please contact us at support@cronofy.com.