Office 365 Shared Folders
Required plan: GrowthOur recommended approach for configuring Enterprise Connect access is to use mailbox impersonation. This offers the simplest configuration for an organization without compromising functionality. Your application will be able to request the required level of control over the user’s or resource calendars to deliver your features.
However, many organizations model resources and group calendars in Shared Folders using Delegate Access. These can also be accessed using an Enterprise Connect authorization.
Whilst the full authorization approach is supported, shared folders access can also be configured with a finer grained set of permissions for the Service Account being used.
There are scenarios where customer IT and security teams will want to restrict your applications access to the data.
Supporting Shared Folder Permissions #
The full list of permissions available are:
- None
- Owner
- PublishingEditor
- Editor
- PublishingAuthor
- Author
- NoneditingAuthor
- Reviewer
- Contributor
- FreeBusyTimeOnly
- FreeBusyTimeAndSubjectAndLocation
These permissions are set at the Calendar level not at the account level. This allows for differing levels of access for individual calendars within an account.
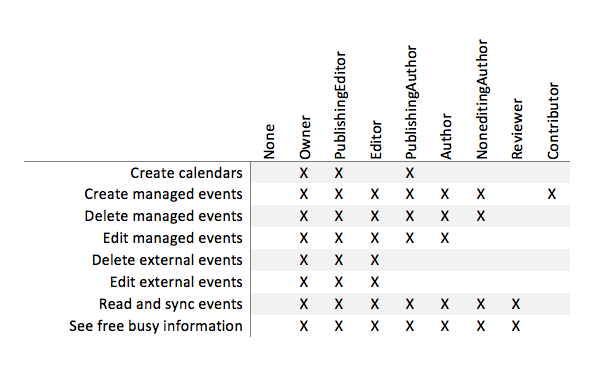
The following table lists the various permissions mapped onto Cronofy functionality.
Please note that the FreeBusy roles do not currently allow Cronofy any access to the Calendar, if you wish to discuss options with regards to this please contact us.
These permissions are set via the Add-MailboxFolderPermission Powershell commands as documented here:
https://technet.microsoft.com/en-us/library/dd298062(v=exchg.150).aspx
It is also possible to set permissions for a folder with a Custom permissions model. This requires some specific help with configuration so let us know if your customer has this set up.
Accessing Shared Folders via the Cronofy API #
Interacting with the contents of the shared folder is the same as for a user or resource mailbox from a Cronofy API perspective. You request delegated access to obtain an access_token and make API requests as needed with that token.
Push notification channels are also supported so your application can receive notifications of any changes to the shared calendar without the need to poll for changes.